Key takeaways:
- Explore 12 best practices to enhance store safety, including surveillance systems and employee training.
- Learn the key aspects of retail store security and its growing importance in 2026.
- Find out how Gofrugal’s GoSecure can help protect your retail store with smart security solutions.
In today's environment, retailers have no choice but to prioritize both physical and digital assets, as understanding what is store security has become a paramount necessity. Each year, inadequate security measures lead to significant financial losses for retailers, yet many still overlook the importance of data as a valuable asset.
As per the Data Breach Investigation Report 2023, small and medium-sized businesses (SMBs) encounter 699 incidents annually, resulting in 381 confirmed cases of data disclosure. In comparison, large businesses experience 496 incidents annually, leading to 227 confirmed cases of data disclosure.
Beyond the tangible losses from theft or fraud, the compromise of sensitive information poses a serious risk. That’s why diving deeper into the crucial intersection of physical and data security and learning how to accomplish both through actionable tips is important.
Contents
What is retail store security?
The importance of store security in the retail industry
Types of retail store security
12 tips to improve retail store security
How Gofrugal can help secure retail stores
What is retail store security?
Retail store security is the combination of physical and digital measures taken to protect both customers and staff while reducing the risk of theft and other security breaches. In today's digital age, retail security has evolved beyond just physical safety to include robust data security measures, as protecting customer and business information has become crucial for any retail operation. It involves a range of strategies such as installing CCTV cameras, employing security personnel, and optimizing store layouts to deter theft.
The importance of store security in retail management
Focusing on store security in retail management is essential for several critical reasons, including:
- Enhanced customer safety – Secure retail environments boost customer confidence and encourage exploration.
- Employee well-being – Security measures create positive workplaces, increasing employee morale.
- Theft deterrence – Surveillance, security personnel, and anti-shoplifting strategies prevent losses.
- Asset safeguarding – Security protects merchandise, equipment, and store infrastructure.
- Legal compliance and trust – Adherence to regulations prevents legal issues and builds customer trust.
- Operational continuity – Robust security ensures uninterrupted business operations.
- Positive brand image – Secure environments contribute to a positive brand reputation.
- Data protection – Securing customer data in the technology-driven retail landscape is essential to protect customers’ information.
Types of retail store security
Retail store security can be broadly classified into two types of store security: physical security and data security.

Physical security
Physical security is crucial for safeguarding tangible aspects within a retail store, ensuring the safety of both assets and individuals. This includes inventory protection and measures to secure and monitor stock, preventing theft or damage. Protection for electrical components, IT hardware, stationary, and racks along with security measures to protect cash, minimize the risk of theft or loss.
Data security
Data security is increasingly critical in the digital age, safeguarding sensitive information related to customers, transactions, and the overall operation of the retail business.
12 tips to improve retail store security
Here are some actionable tips that will help you improve your retail store security and increase your brand reputation among customers.

1. Cash handling
A critical yet often overlooked aspect of retail store security is the meticulous handling of cash transactions. Here’s what you can do to improve this:
- Enable automatic cash drawer opening after transactions to minimize manual handling and enhance efficiency.
- Enhance cash security by integrating biometric technology with access codes for cash lockers, adding an extra layer of protection.
- Set up a routine for daily payment settlements to banks, reducing the amount of cash stored on-site and mitigating risks.
- Promote 100% digital payments to suppliers and vendors, reducing the reliance on physical cash transactions.
- Conduct frequent bank reconciliation statements (BRS) or automate the process to promptly identify discrepancies.
- Implement a systematic approach to petty cash and employee expense management, including a stringent approval process.
- Exercise control over bill editing and cancellation to prevent unauthorized alterations to financial records.
- Conduct regular checks on supplier and customer credit limits to manage potential risks associated with credit transactions.
2. Access control systems
Implement electronic access control systems such as biometrics for attendance, biometrics for cold storage, and passcodes and biometric access for cash lockers to restrict unauthorized entry to specific areas. These systems enhance overall security by managing and monitoring access points effectively. Choose the right business management software that has a hierarchical access management and role management system. This includes customizable privileges for staff, department heads, managers, proprietors, and the like.
3. Effective surveillance practices
Maintaining a vigilant eye through strategic surveillance practices is integral when enhancing retail store security. Consider the following tips to optimize your CCTV system:
- Schedule a weekly review of CCTV footage to identify and address any anomalies promptly.
- Make external backups of recordings to safeguard against system failures or tampering. Additionally, extend the retention period to a minimum of six months, surpassing the common practice of deleting footage after 60 days.
- Ensure meticulous camera placement to cover 100% of the store landscape. Periodically verify and align camera positions to eliminate potential blind spots that could be exploited by individuals seeking to engage in theft.
4. Security personnel training
Empower your security personnel with hands-on, practical strategies that resonate with everyday scenarios. Here are some relatable practices they can learn and implement:
- Encourage the use of barcode-based bill scanning during checkout instead of manual bill punching.
- Provide training on reacting to RFID magnetic tag detections at exit points. Equip security personnel with the skills to identify and address potential shoplifting incidents, enhancing overall theft prevention efforts.
- Train personnel to conduct thorough scans of items as customers enter the store. Emphasize the importance of quickly identifying and segregating any suspicious items, maintaining a proactive stance against potential security threats.
- Focus on enhancing communication skills, teaching security personnel to interact with customers, colleagues, and law enforcement effectively.
5. Emergency preparedness and response
Develop and regularly practice emergency response plans with employees. This includes procedures for various scenarios such as theft, natural disasters, or other security breaches, ensuring a swift and coordinated response.
- Conduct thorough fire emergency training sessions for all employees. This includes understanding the proper use of fire extinguishers, evacuation procedures, and the importance of remaining calm during such incidents.
- Regularly practice fire evacuation drills to familiarize employees with exit routes and assembly points. Consistent drills contribute to a more efficient and organized evacuation in the event of a real emergency.
- Ensure all employees are aware of emergency contact information and communication protocols.
- Familiarize employees with the location and proper usage of fire safety equipment such as fire extinguishers, fire alarms, and emergency exits.
- Provide basic first aid training to employees, emphasizing the importance of immediate response to injuries or smoke inhalation during a fire emergency.
6. Daily stock auditing
Get an efficient and error-free inventory stock-taking app, such as GoSure StockTake, designed for perpetual stock counting. It ensures an instant review of discrepancies and immediate stock correction, minimizing the chances of internal theft and guaranteeing accurate record keeping. Achieve an accurate and quick audit of any item at any location in your store.
7. Perimeter security
Secure the store’s perimeter with measures like fences, lighting, and surveillance to deter external threats. This creates an additional layer of protection for inventory and assets.
8. Understanding data vulnerabilities
Conduct a thorough assessment of potential data vulnerabilities within the business. Identify and address weak points in data storage, transmission, and processing to fortify against potential breaches.
- Examine where your data resides. Is it on local servers, in the cloud, or both? Identify potential risks associated with each storage option.
- How is data moving within your business? Look at networks and communication channels. Ensure data in transit is encrypted to prevent interception.
- Assess how your systems handle data. Pinpoint areas where sensitive information is processed. This could be at payment gateways, user logins, or data analytics points.
9. Data encryption protocols
Implement robust data encryption protocols for sensitive customer and business information. Encryption adds an extra layer of protection, making it more challenging for unauthorized individuals to access and misuse data.
10. Continuous software maintenance for enhanced security
Regular updates serve as a proactive measure in fortifying your security posture and mitigating potential risks associated with evolving cyber threats. If you have point-of-sale (POS) software, regularly update and patch POS software to address vulnerabilities and ensure the latest security features are in place.
Regularly update and patch not only POS software but also antivirus programs, CCTV surveillance audit software, and operating systems. Keeping all software up to date is essential to address vulnerabilities and incorporate the latest security features. This comprehensive approach ensures a more robust defense against potential security threats across multiple fronts, contributing to the overall resilience of your business systems.
11. Employ multi-factor authentication (MFA)
Increase POS security by implementing multi-factor authentication, requiring additional verification steps beyond passwords.
12. Integrated payment device with billing software
Achieve secure transactions by integrating payment devices with your billing software. Surprisingly, less than 20% of businesses leverage this game-changing step, making it an overlooked first line of defense against payment thefts.
Having an integrated payment device connects your billing operations with secure payment gateways. This not only enhances efficiency, but also sets the stage for a robust defense against potential threats.
Once you’ve completed integrated payments, take it a step further with end-to-end encryption. Safeguard transaction data from start to finish, ensuring every piece of sensitive information is shielded against prying eyes.
End-to-end encryption becomes the guardian of your transactions, making it significantly harder for any unauthorized entities to intercept or manipulate data during its journey from the payment device to the secure gateway.
How Gofrugal can help secure retail stores
Gofrugal empowers businesses by safeguarding assets and ensuring the security of crucial business operations. Here’s how Gofrugal enhances retail store security.
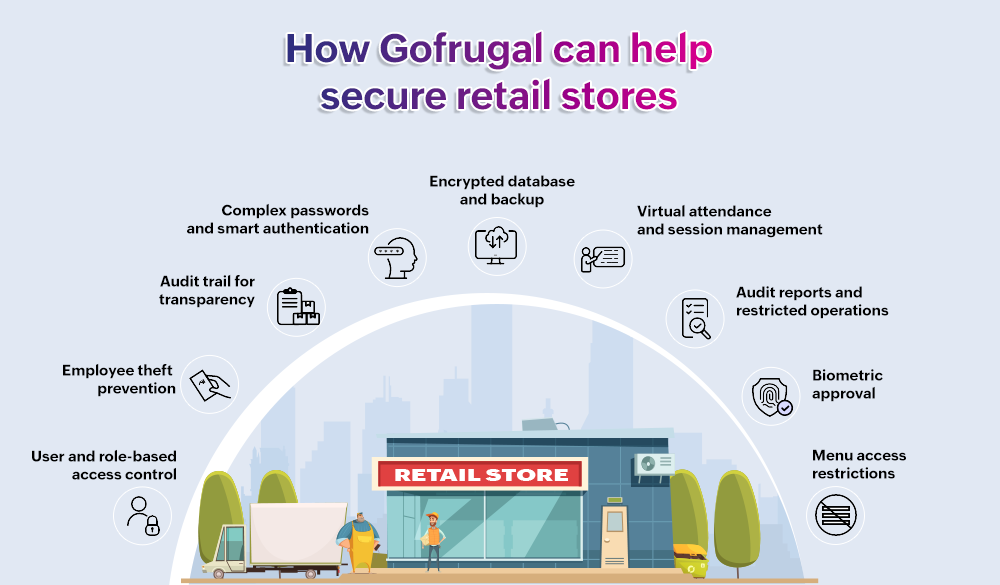
User and role-based access control
Prevent unauthorized access to sensitive business information by implementing user and role-based access controls, ensuring that only authorized personnel have access to specific data and functionalities.
Employee theft prevention
Mitigate the risk of employee theft and inventory shrinkage through approval mechanisms, real-time alerts, and instant notifications for key operations. This proactive approach enhances overall security in daily operations.
Audit trail for transparency
Document every operation executed in the POS system with an audit trail, allowing for the tracking and review of activities. This transparency is crucial for identifying and addressing any suspicious or irregular activities.
Complex passwords and smart authentication
Implement complex password combinations and SmartAuth with multi-factor authentication (MFA) for biometric-based password-less sign-ins, adding robust layers of protection against unauthorized access.
Encrypted database and backup
Ensure data security by utilizing encrypted databases and providing backup options in both local and cloud storage. This protects against insider threats, cyberattacks, ransomware, and other potential data vulnerabilities.
Virtual attendance and session management
Track individual employee login hours, billings, sale returns, and cash transactions accurately through virtual attendance. Session management allows centralized tracking of all counters, enhancing operational visibility.
Audit reports and restricted operations
Generate detailed audit reports for user activities, especially transactions, offering complete control over employee actions. Restrict users from performing unwanted operations, seeking owner approval through the WhatsNow mobile solution, if necessary.
Biometric approval
Adds an extra layer of security with biometric approval, ensuring that restricted operations cannot be carried out without the owner’s explicit consent, enhancing overall security and control.
Menu access restrictions
Restrict users from accessing menus that are not relevant to their roles, ensuring that confidential data is accessible only to authorized individuals. Password protection further secures specific menus and screen operations.
To learn more about Gofrugal’s security management features, click here!
Don’t miss out on double data protection
Unforeseen challenges like natural calamities, hardware failures, or data loss can jeopardize your operations. With Gofrugal’s GoSecure, cloud-based data backup software, you get more than just a backup–you get peace of mind.
Why GoSecure?
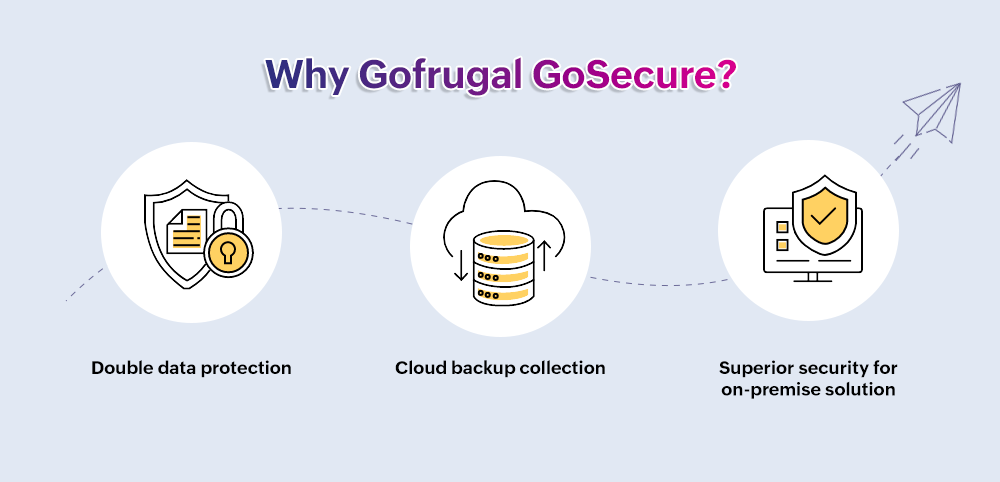
Double data protection: GoSecure ensures your business data is not just backed up, but it’s doubly protected—twice the security, double the peace of mind.
Cloud backup collection: No more manual backups! GoSecure automatically backs up your crucial POS data to the cloud in no time. Whether you’re facing a virus attack or a natural disaster, your valuable data remains safe and sound.
Superior security for on-premise solutions: Provide a dedicated cloud backup tool for on-premises solutions. GoSecure is not just a backup tool; it’s your shield against data disasters.
While being physically present in the store 24/7 may not be feasible, there’s a practical solution at hand: investing in security for retail stores and implementing strategies that effectively handle the task. This not only provides peace of mind but also enhances overall security and operational efficiency.



